背景介绍
近期,我们监控到一起针对 Base 上的项目CloberDEX的链上攻击事件,
https://basescan.org/tx/0x8fcdfcded45100437ff94801090355f2f689941dca75de9a702e01670f361c04
被攻击的项目为 CloberDEX ,攻击者通过此次攻击获利约为 133 ETH ,约为 500,000 USD 。该项目的主要功能如下:open 开一个新交易池包含 A 到 B 和 B 到 A 的交易对,同样每个交易对包含预设的交易策略;mint 为给交易对添加流动性并获得 LP Token ;burn 为销毁 LP Token 获得对应的货币。
攻击及事件分析
首先,攻击者从 Morpho Blue 中利用 flashloan 借贷了267个WETH,
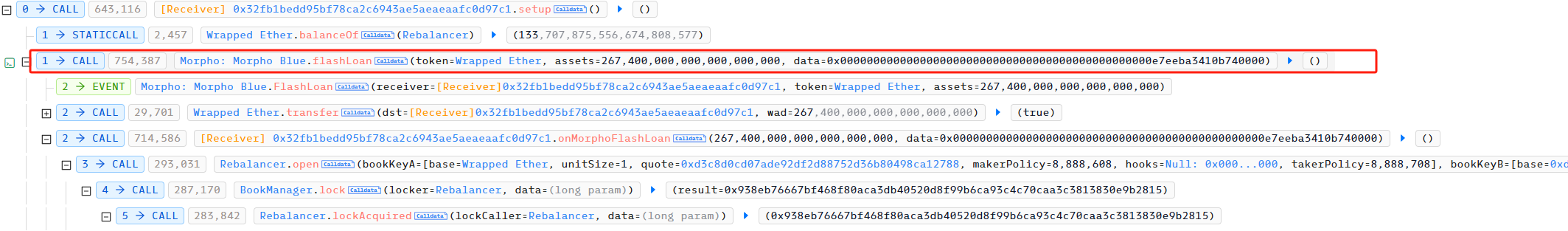
接着,攻击者使用 open 在 CloberDEX 开了两个交易对分别是 Token/WETH 和 WETH/Token ,其中, Token 为攻击者自行部署的合约。

然后,攻击者利用 mint 分别向刚开的交易对中转入 267 WETH 和 267 Token ,用于添加流动性并获取 LP Token。

至此,都没问题。最后,攻击者利用 burn 销毁刚获得的LP Token,我们看一下 burn 的具体实现;
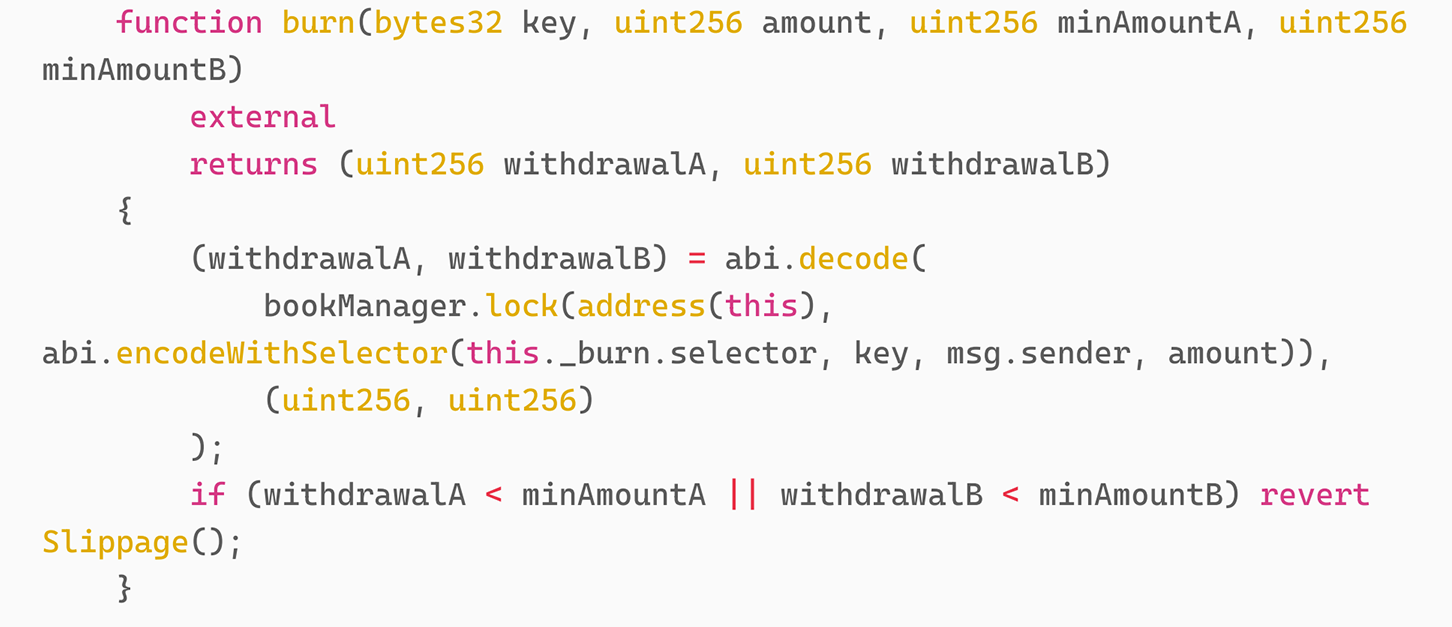
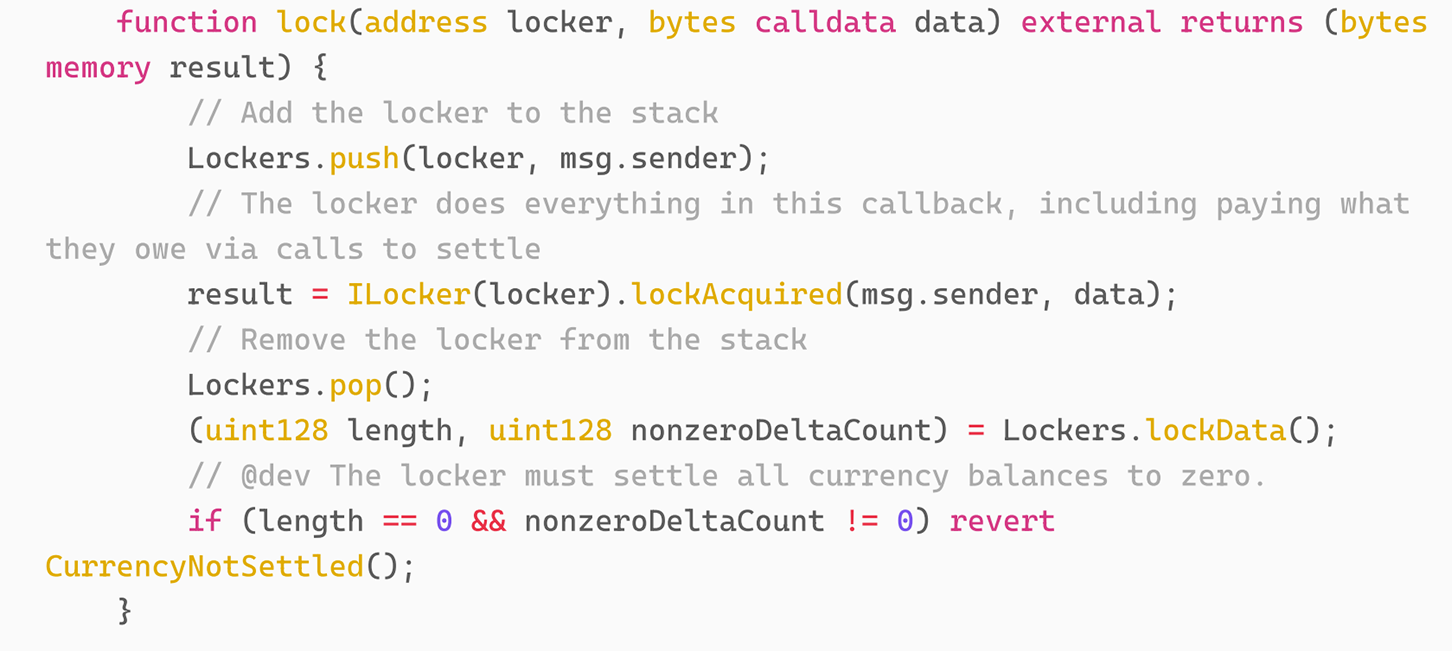
控制流走向了 lock 函数,同样,我们看一下 lock 的具体实现;
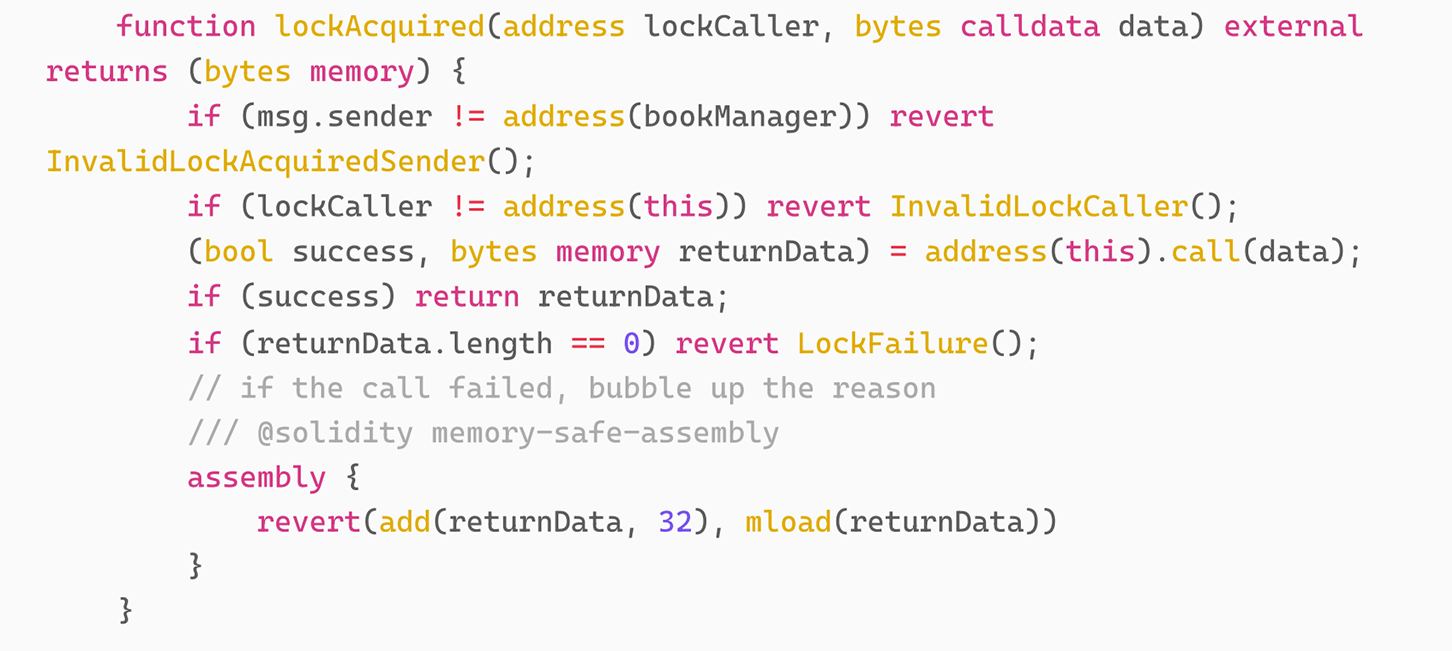
可以看到,lock 函数中又把 bytes caldata data 传向了 lockAcquired 函数,我们继续看该函数的实现;
我们发现这行代码
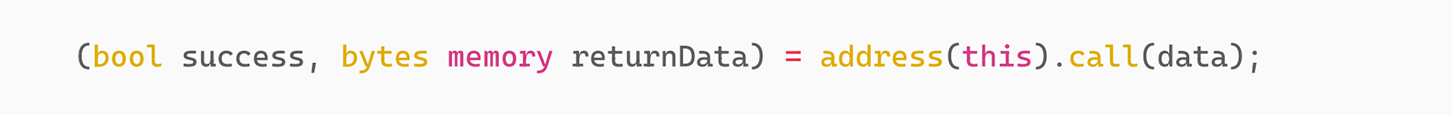
我们可以看到,该代码调用的函数由 data 决定。那么 data 的前四字节此时为 _burn 的签名,所以本质上 burn 调用了 _burn 。
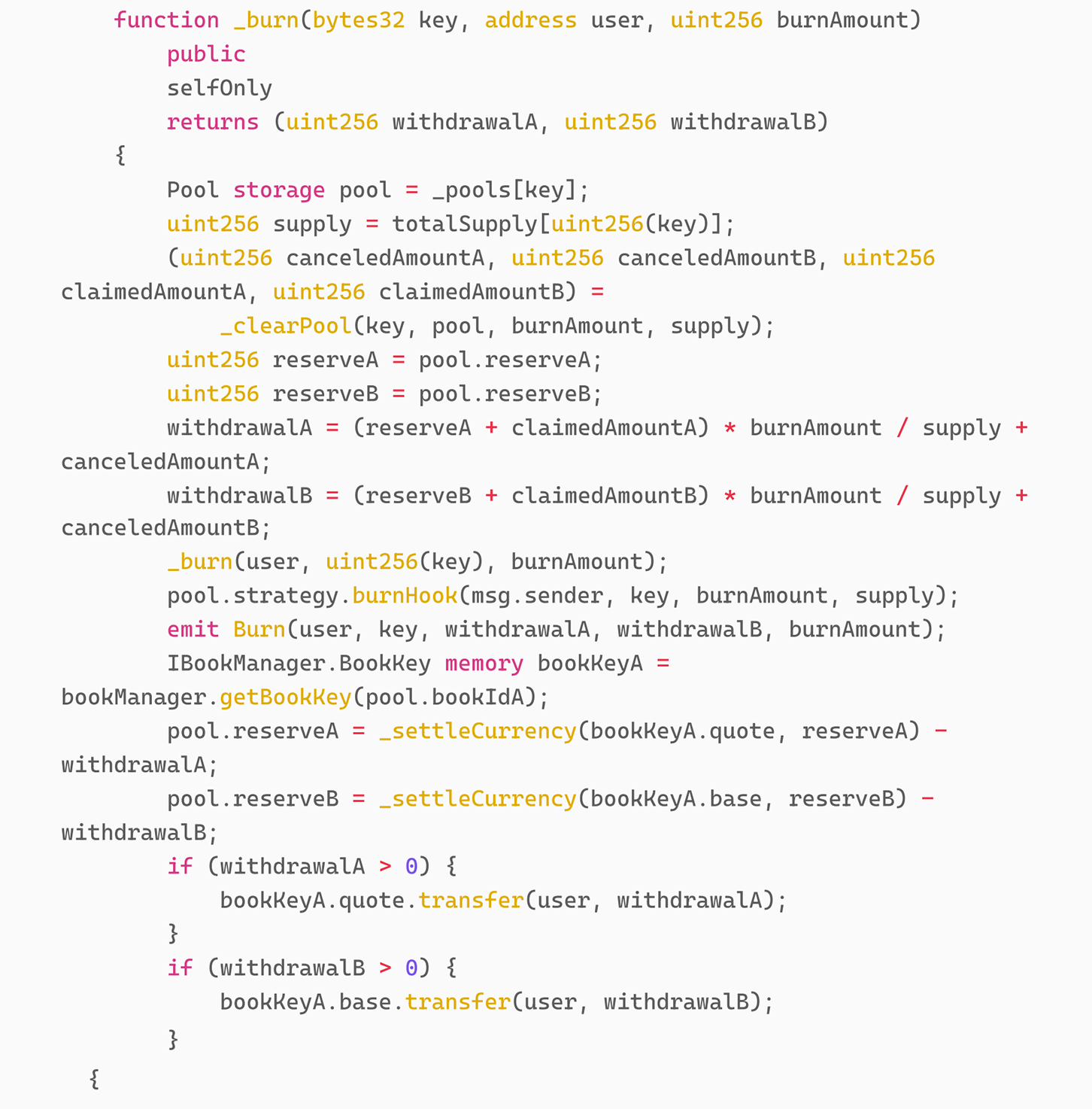
我们可以看到, _burn 又调用了 pool.strategy.burnHook(msg.sender, key, burnAmount,supply) ,而且,针对 pool 的 reserver 的处理又在该代码之后。所以,问题出现在这里,交易对对应的 pool 的 strategy 合约的地址可以由攻击者控制。在此次攻击中,攻击者将该地址写为自己的攻击合约地址即:0x32fb1bedd95bf78ca2c6943ae5aeaeaafc0d97c1。
当合约流程走到了攻击合约的 BurnHook 中后,又继续调用 burn 完成重入攻击。
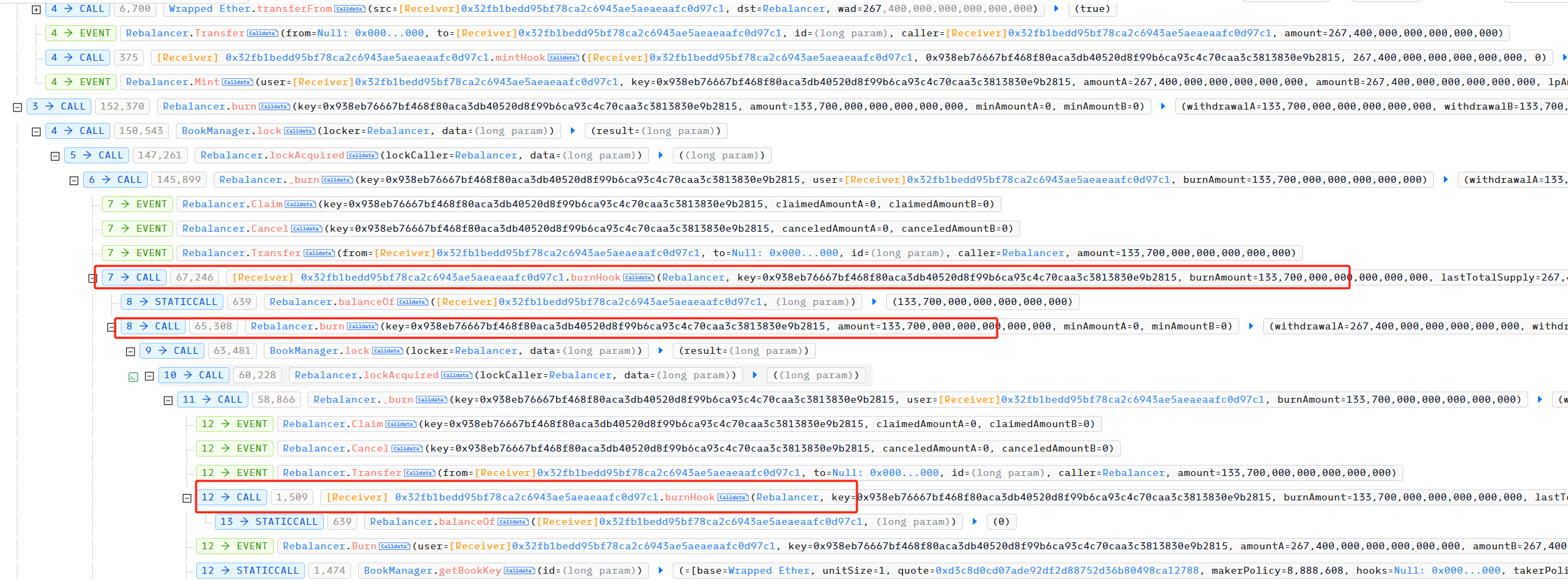
攻击者通过该漏洞取出了投入的 264 个 WETH 和 CloberDEX 合约中的 133 个 WETH ,在归还flashloan 的贷款后获利 133.7 ETH ,约为 500,000 USD 。
总结
本次漏洞成因主要是因为 CloberDEX 项目方合约在获取销毁 LP Token 的代码中没有进行重入检测和防护,且更新状态变量在合约调用之后,最终导致攻击者利用该重入漏洞掏空项目方的WETH 。建议项目方在设计经济模型、价格计算机制和代码运行逻辑时要多方验证,合约上线前审计时尽量选择多个审计公司交叉审计。